KMU Information Securiy Policy
出自KMU Wiki
(修訂版本間差異)
| 在2013年11月29日 (五) 08:57所做的修訂版本 (編輯) Cch (對話 | 貢獻) ←上一個 |
在2013年11月29日 (五) 09:07所做的修訂版本 (編輯) (撤銷) Cch (對話 | 貢獻) 下一個→ |
||
| 第1行: | 第1行: | ||
| <pre> | <pre> | ||
| - | + | Kaohsiung Medical University Information Security Policy | |
| Document No. IS-A-001 | Document No. IS-A-001 | ||
| 第24行: | 第24行: | ||
| 2.2 Information security organization | 2.2 Information security organization | ||
| 2.3 Information asset classification and control | 2.3 Information asset classification and control | ||
| - | 2.4 Safety of personnel management and training | + | 2.4 Safety of personnel management and training |
| - | 2.5 Physical and environmental security | + | 2.5 Physical and environmental security |
| - | 2.6 Communication and job security management | + | 2.6 Communication and job security management |
| - | 2.7 Access control security | + | 2.7 Access control security |
| - | 2.8 Safety system development and maintenance | + | 2.8 Safety system development and maintenance |
| - | 2.9 Information security incident response and handling | + | 2.9 Information security incident response and handling |
| - | 2.10 Business continuity operations management | + | 2.10 Business continuity operations management |
| - | 2.11 Regulations and compliance policy implementation units | + | 2.11 Regulations and compliance policy implementation units |
| - | Our school 's internal staff, outsourcing vendors and visitors and should comply with this policy . | + | Our school 's internal staff, outsourcing vendors and visitors and should comply with this policy. |
| 3. TARGET | 3. TARGET | ||
| 第40行: | 第40行: | ||
| user data privacy. With all my colleagues in common Efforts to achieve the following objectives: | user data privacy. With all my colleagues in common Efforts to achieve the following objectives: | ||
| - | 3.1 Protection of our business activities information from unauthorized access . | + | 3.1 Protection of our business activities information from unauthorized access. |
| - | 3.2 Protection of our business activities information from unauthorized modifications to ensure that it is correct and complete . | + | 3.2 Protection of our business activities information from unauthorized modifications to ensure that it is |
| - | 3.3 IT business continuity establish operational plans to ensure the continued operation of our business activities . | + | correct and complete. |
| - | 3.4 School 's activities shall comply with the implementation of the requirements of relevant laws or regulations . | + | 3.3 IT business continuity establish operational plans to ensure the continued operation of our business |
| + | activities. | ||
| + | 3.4 School 's activities shall comply with the implementation of the requirements of relevant laws or | ||
| + | regulations. | ||
| 4. RESPONSIBILIEY | 4. RESPONSIBILIEY | ||
| - | 4.1 School's management to establish and review this policy. | + | 4.1 School's management to establish and review this policy. |
| - | 4.2 Information security managers through appropriate standards and procedures to implement this policy. | + | 4.2 Information security managers through appropriate standards and procedures to implement this policy. |
| - | 4.3 All personnel and outsourcing services vendors are required in accordance with relevant safety management procedures to maintain information security policies. | + | 4.3 All personnel and outsourcing services vendors are required in accordance with relevant safety management |
| - | 4.4 All officers are responsible for reporting information security incidents and of any identified weaknesses. | + | procedures to maintain information security policies. |
| - | 4.5 Any compromise information security behavior , depending on the seriousness will pursue its legal responsibility and administrative responsibility according to the school or the relevant provisions of punishment . | + | 4.4 All officers are responsible for reporting information security incidents and of any identified weaknesses. |
| + | 4.5 Any compromise information security behavior , depending on the seriousness will pursue its legal | ||
| + | responsibility and administrative responsibility according to the school or the relevant provisions of | ||
| + | punishment . | ||
| 5. REVIEW | 5. REVIEW | ||
| - | This policy should be reviewed at least annually once only , to reflect the government decree , the latest technology and business development status , to ensure that the school forever | + | This policy should be reviewed at least annually once only , to reflect the government decree , the latest |
| - | Continued operation of network services and the provision of academic ability . | + | technology and business development status , to ensure that the school forever Continued operation of network |
| + | services and the provision of academic ability . | ||
| 6. IMPLEMENTATION | 6. IMPLEMENTATION | ||
| - | 6.1 Information security policy management review meetings with the information security policy audits. | + | 6.1 Information security policy management review meetings with the information security policy audits. |
| - | 6.2 This policy will be "Information Security Committee" after the implementation of the resolutions , amendments are made. | + | 6.2 This policy will be "Information Security Committee" after the implementation of the resolutions , |
| + | amendments are made. | ||
| </pre> | </pre> | ||
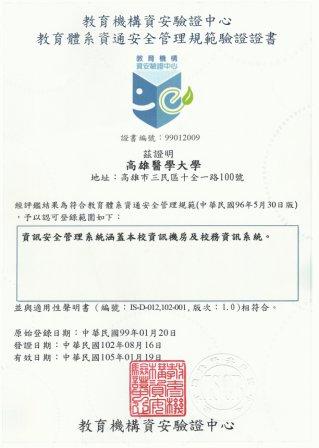
| [[Image: KMU-EDU-ISMS-Cert2013.jpg]] | [[Image: KMU-EDU-ISMS-Cert2013.jpg]] | ||
在2013年11月29日 (五) 09:07所做的修訂版本
Kaohsiung Medical University Information Security Policy
Document No. IS-A-001
Confidentiality level general
Revision 1.3
1. OBJECTIVE
The set of policies aimed at ensuring Kaohsiung Medical University (hereinafter referred to as the school)
belongs information assets confidentiality, integrity and availability, and comply with the requirements of
relevant laws and regulations, harmless from internal and external threat of deliberate or accidental .
2. SCOPE
Information security management covers 11 management issues, to avoid human error, deliberate or natural
disasters and other factors, resulting information is not When using, leakage, tampering, destruction,
violations occur, our school has brought a variety of possible risks and hazards. Management issues are as
follows:
2.1 Information security policy setting and evaluation
2.2 Information security organization
2.3 Information asset classification and control
2.4 Safety of personnel management and training
2.5 Physical and environmental security
2.6 Communication and job security management
2.7 Access control security
2.8 Safety system development and maintenance
2.9 Information security incident response and handling
2.10 Business continuity operations management
2.11 Regulations and compliance policy implementation units
Our school 's internal staff, outsourcing vendors and visitors and should comply with this policy.
3. TARGET
Maintain the confidentiality of our information assets , integrity and availability , and protect
user data privacy. With all my colleagues in common Efforts to achieve the following objectives:
3.1 Protection of our business activities information from unauthorized access.
3.2 Protection of our business activities information from unauthorized modifications to ensure that it is
correct and complete.
3.3 IT business continuity establish operational plans to ensure the continued operation of our business
activities.
3.4 School 's activities shall comply with the implementation of the requirements of relevant laws or
regulations.
4. RESPONSIBILIEY
4.1 School's management to establish and review this policy.
4.2 Information security managers through appropriate standards and procedures to implement this policy.
4.3 All personnel and outsourcing services vendors are required in accordance with relevant safety management
procedures to maintain information security policies.
4.4 All officers are responsible for reporting information security incidents and of any identified weaknesses.
4.5 Any compromise information security behavior , depending on the seriousness will pursue its legal
responsibility and administrative responsibility according to the school or the relevant provisions of
punishment .
5. REVIEW
This policy should be reviewed at least annually once only , to reflect the government decree , the latest
technology and business development status , to ensure that the school forever Continued operation of network
services and the provision of academic ability .
6. IMPLEMENTATION
6.1 Information security policy management review meetings with the information security policy audits.
6.2 This policy will be "Information Security Committee" after the implementation of the resolutions ,
amendments are made.